So, how do you know you're protecting your organization? What do you do to measure your success? This domain describes various methods, techniques, and the process of assessing security
- NIST 800-53A: Building Effective Assessment Plans
- NIST 800-137: Information Security Continuous Monitoring (ISCM)
- NIST 800-115: Technical Guide to Information Security Testing and Assessment
- Unit Testing: Low-level test of software components, such as functions, procedures, or objects.
- Installation Testing: Testing software as its install and first operated
- Integration testing: Testing multiple software components as they're combined intoa working system.
- Regression Testing: Testing software after updates, modifications, or patches
- Acceptance Testing: Testing to ensure the software meets the customers operational requirements. Referred to as user Acceptance testing, when done by the customer.
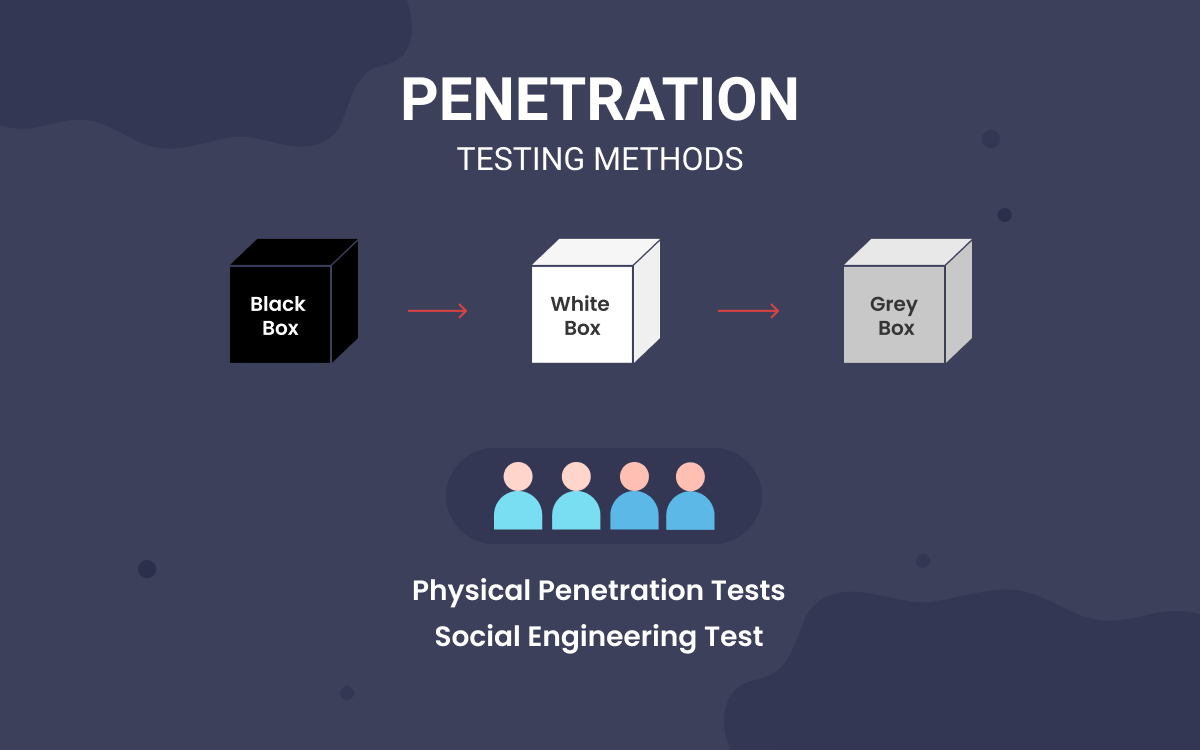
- Fuzzing: Used in black-box testing. Sending ramdom malformed data as inputs into programs to determine if they will crash. One of the first steps of discovering Buffer Overflow
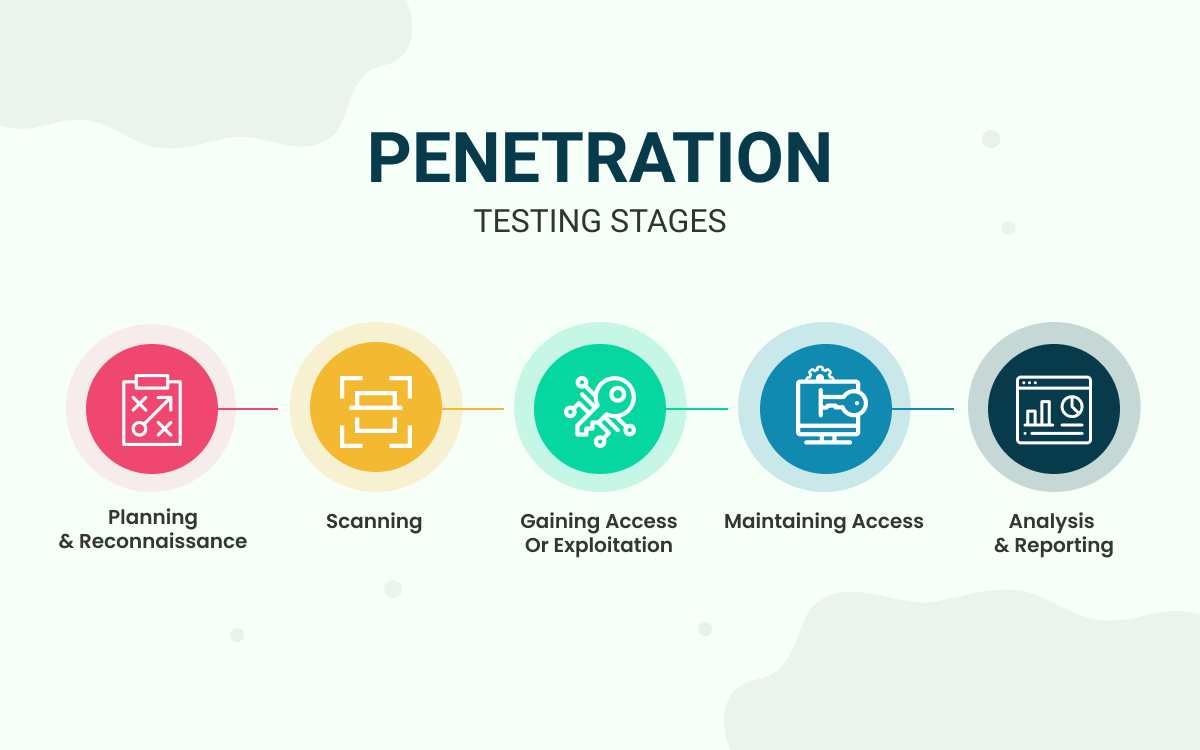
- Planning
- Reconnaissance
- Scanning
- Vulnerability Assessment
- Exploittation
- Reporting:
- Spoofing: Impersonating someone or something
- Tampering: Modifying data or code
- Repudiation: Claiming to have not performed an action
- Information Disclosure: Exposing information to someone unauthorized
- Denial of Service: Deny or degrade service to users
- Elevation of Prilege: Gain capabilites without being authorized